Is Proton VPN Safe? A Deep Dive Into Its Security and Privacy
Eneba Hub contains affiliate links, which means we may earn a small commission if you make a purchase through them—at no extra cost to you. Learn more

Is Proton VPN safe? Yes, it actually is. And unlike most VPNs that just say “trust us,” Proton can back it up.
Built by the same team of scientists who created Proton Mail at CERN, Proton VPN has established itself as one of the most transparent and verifiable VPN services available. It publishes its code, undergoes regular independent audits, and operates under Swiss jurisdiction.
In this guide, I’ll examine Proton VPN’s safety from every angle: encryption standards, logging policies, jurisdiction, audits, and real-world legal tests. By the end, you’ll have a complete picture of whether Proton deserves your trust.
Jump to:
Quick Overview: Proton VPN Security at a Glance

| Security Feature | Proton VPN Status | Details |
|---|---|---|
| Jurisdiction | Switzerland | Outside 5/9/14 Eyes, no mandatory logging laws |
| No-Logs Audits | 4 consecutive annual audits | Securitum (2022, 2023, 2024, 2025) |
| Real-World Test | Passed (2019) | Court order received, no logs to provide |
| Encryption | AES-256/ChaCha20 | Military-grade with perfect forward secrecy |
| Protocols | WireGuard, OpenVPN, IKEv2 | No weak or dangerous protocols (PPTP/L2TP excluded) |
| Open Source | 100% on all platforms | Windows, macOS, Linux, iOS, Android |
| Kill Switch | All platforms | Standard + Advanced modes available |
| DNS Leak Protection | Built-in | Proton-operated DNS servers |
| Multi-Hop | Secure Core | Routes through Switzerland, Iceland, Sweden |
| Server Network | 15,000+ servers | 120+ countries, bare-metal only |
| Ownership | Proton Foundation (non-profit) | No VC investors, fully transparent |
Swiss Jurisdiction: Why Location Matters
Proton VPN is headquartered in Geneva, Switzerland, and this isn’t just a marketing point. Switzerland offers VPN users several critical advantages that directly impact your privacy.
Switzerland sits outside both EU and US jurisdictions, meaning it’s not subject to the surveillance frameworks that govern VPN providers in those regions. More importantly, Switzerland is not a member of the 5, 9, or 14 Eyes intelligence-sharing alliances.
Under Swiss law, Proton VPN has no mandatory data retention requirements. The company can’t be legally compelled to start logging user activity, unlike providers in most other countries where courts can order VPNs to begin monitoring specific users. Switzerland also requires that surveillance targets eventually be notified, giving them the opportunity to contest data requests in court.
Proton VPN can only respond to legally binding requests from Swiss courts, and foreign requests must go through formal international legal channels before Switzerland will consider them. Even then, Proton can only provide data it actually has, which leads to the next critical point.
For a deeper look at how jurisdiction affects VPN privacy claims, our best-rated VPN for protecting data guide compares legal frameworks across providers.
No-Logs Policy: Verified Four Times
Every VPN claims a “no-logs policy,” but these claims mean nothing without independent verification. Proton VPN has submitted its infrastructure to annual third-party audits by Securitum, a leading European cybersecurity firm that conducts over 300 security testing projects annually for major corporations and banks.
The most recent audit, published in September 2025, marked the fourth consecutive year of no-logs verification. Securitum security experts spent several days on-site reviewing VPN configuration files, server configurations, operating procedures, and interviewing staff. Their examination covered:
- Whether user activity is tracked or logged on production VPN servers
- Whether connection metadata like DNS queries or session timestamps are stored
- Whether network traffic is inspected or logged
- Whether information about specific services users connect to is monitored
The audit conclusion was unambiguous: no instances of user activity logging, connection metadata storage, or network traffic inspection were found that would contradict the no-logs policy. The auditors verified that robust administrative and technical controls ensure continuous integrity of the no-logging environment.
What separates Proton from many competitors is that these full audit reports are published publicly on their website. Unlike some VPNs that require you to sign non-disclosure agreements before viewing audit results, Proton’s commitment to transparency means anyone can verify their claims.
Real-World Legal Test: The 2019 Case
Audits are valuable, but nothing proves a no-logs policy like real-world legal pressure. In 2019, Proton VPN’s claims were tested when they received a court order to turn over logs that would help identify a user. Proton was unable to comply with the request because the logs simply didn’t exist.
This incident confirmed that Proton’s no-logs infrastructure works as designed. Even when legally compelled to provide user data, there was nothing to hand over. The company publishes a transparency report documenting legal requests, maintaining accountability while demonstrating that their privacy protections hold up under pressure.
Encryption Standards: Military-Grade

Proton VPN encrypts all network traffic using either AES-256 or ChaCha20, depending on which VPN protocol you use. Both ciphers are considered extremely secure by cryptographic standards.
For OpenVPN and IKEv2 connections, Proton uses AES-256 encryption. Breaking AES-256 through brute force would take even the most advanced computers billions of years. The control channel establishing your VPN connection uses AES-256-GCM for its symmetric cipher, RSA-4096 for the key exchange, and HMAC SHA-384 for hash authentication.
WireGuard connections use ChaCha20 encryption, which is just as secure as AES-256 but performs slightly faster on devices without hardware AES acceleration. This makes WireGuard the recommended protocol for most users, delivering excellent security without sacrificing speed.
All connections use perfect forward secrecy through Diffie-Hellman key exchange. This means each VPN session generates unique encryption keys. If a future session is somehow compromised, your past sessions remain secure because different keys were used. Understanding these encryption standards can help you pick the best VPN for privacy and speed that actually delivers on security promises.
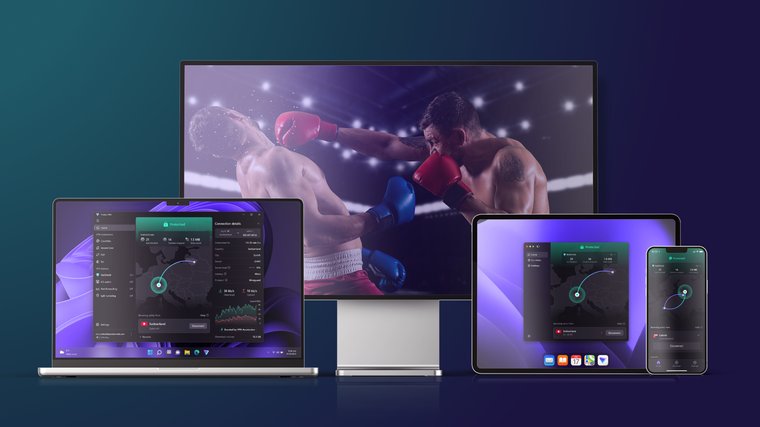
VPN Protocols: Only the Secure Options
Proton VPN exclusively uses protocols with proven security track records: WireGuard, OpenVPN, and IKEv2. They deliberately exclude older protocols like PPTP that have known security vulnerabilities, even though these would be cheaper and easier to operate.
WireGuard is the default protocol and recommended for most users. Its lean 4,000-line codebase is easier to audit than OpenVPN’s 70,000+ lines, reducing potential attack surface while delivering faster connections. WireGuard also handles network switching smoothly, maintaining your VPN connection when moving between WiFi and cellular networks. It’s the best VPN protocol for torrenting, gaming, and many other activities.
OpenVPN remains valuable for bypassing censorship. When configured to run over TCP port 443, OpenVPN traffic becomes difficult to distinguish from regular HTTPS traffic, making it effective at defeating VPN blocks. Proton’s custom Stealth protocol, built on WireGuard tunneled over TLS, takes this further by masking VPN use against even advanced deep packet inspection techniques.
Open-Source Apps: Full Transparency
Proton VPN was the first VPN provider to open-source apps on all major platforms: Windows, macOS, Android, iOS, and Linux. Every line of code is publicly available for inspection on their GitHub repositories. This transparency allows security researchers worldwide to scrutinize their implementation and identify potential vulnerabilities.
Open-source code provides security through transparency rather than obscurity. When code is heavily scrutinized by the global security community, potential vulnerabilities are spotted and fixed quickly. In contrast, proprietary code may contain security flaws known only to malicious actors who exploit them secretly. This level of transparency is exactly what I’m looking for when considering the best VPNs for cybersecurity needs.
Beyond making code public, Proton has commissioned independent security audits covering all their applications. SEC Consult, a respected security firm, conducted thorough reviews of the codebase. The audits found no vulnerabilities that would allow attackers to break Proton VPN’s encryption or access user data.
Server Infrastructure: Full-Disk Encryption
Some VPN providers heavily market “RAM-only servers” as a security feature. Proton VPN takes a different approach, using full-disk encryption on all servers instead.
RAM-only servers only provide security benefits if the server is powered off. If an adversary gains access to a running machine, whether through physical seizure or remote compromise, they can access all data stored on the server regardless of whether it uses RAM or hard drives. Full-disk encryption protects server certificates, configurations, and software, even if someone gains physical access to a data center.
What truly protects user data is having no logs to access in the first place. Proton’s annually audited no-logs policy means that even if a server were compromised, there’s no user activity data stored to steal. Combined with Swiss jurisdiction preventing forced logging and regular independent audits, this provides robust protection regardless of the storage medium.
Proton VPN operates over 15,000 servers across more than 120 countries, all bare-metal (physical, not virtual) servers under their direct control. This allows them to manage security from the base operating system level, preventing the risks associated with shared virtual infrastructure.
Kill Switch: Protecting Against Leaks
A kill switch is essential for preventing accidental IP exposure if your VPN connection drops. Proton VPN includes kill switch functionality on all supported platforms: Windows, macOS, iOS, iPadOS, Linux, and Android. A reliable kill switch is one of the things that separate the best VPNs out there from all the rest.
On Windows and Linux, Proton offers both standard and advanced kill switch modes. The standard kill switch blocks all traffic during accidental VPN disconnections until the connection can be re-established. It protects you while switching servers and during temporary network issues.
The advanced kill switch goes further, preventing any internet connection without an active VPN. It persists through device restarts and ensures you never accidentally browse unprotected. This mode is particularly valuable for users who need constant protection, such as journalists or activists operating in hostile environments.
Android 8.0+ includes a built-in Always-On VPN and Kill Switch setting that works similarly to the advanced kill switch, blocking all connections unless the VPN is active.
For DNS leak protection, Proton VPN runs its own DNS servers and routes all DNS queries through the encrypted VPN tunnel. Your ISP never sees which websites you’re trying to access because DNS lookups are handled entirely within Proton’s infrastructure. You can verify this protection using sites like dnsleaktest.com while connected.
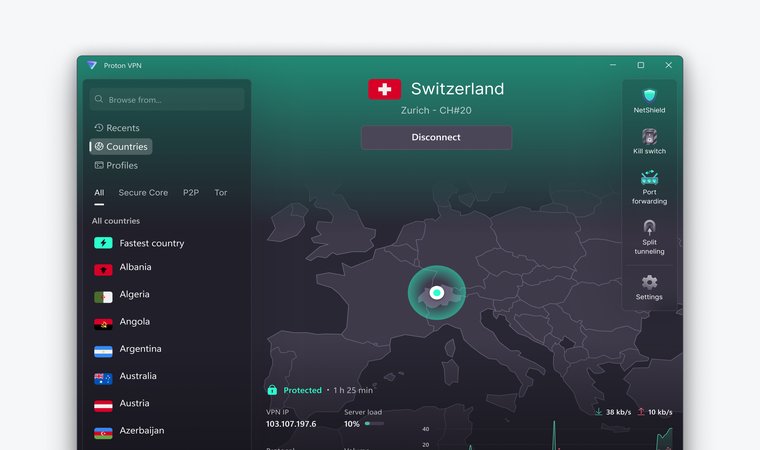
Secure Core: Defense in Depth

Secure Core is Proton VPN’s multi-hop feature that routes your traffic through specially hardened servers before exiting to your final destination. These Secure Core servers are located in privacy-friendly jurisdictions: Switzerland, Iceland, and Sweden.
Unlike regular VPN connections where you connect directly to an exit server, Secure Core routes your traffic through Proton-owned infrastructure in countries with strong legal protections first. Even if an exit server were somehow compromised or monitored, attackers would only see traffic coming from the Secure Core server, not your real IP address.
Secure Core servers are stored in high-security data centers with strict access protocols, reducing the risk of physical tampering. For users facing advanced threats, such as those operating in countries with sophisticated surveillance capabilities, Secure Core provides an additional layer of protection that standard VPN connections can’t match.
This multi-hop approach does add some latency, so it’s not ideal for activities requiring the lowest possible ping. But for browsing, communications, and any situation where security matters more than speed, Secure Core offers meaningful additional protection.
Additional Security Features
Beyond core VPN functionality, Proton VPN includes several features that enhance overall security.
- NetShield is a DNS-based filtering feature that blocks ads, trackers, and known malicious domains. By preventing your browser from loading content from known malware hosts, NetShield provides an additional layer of protection while also speeding up browsing by reducing unnecessary data transfer.
- VPN Accelerator is a set of technologies unique to Proton that can increase VPN speeds by up to 400% when connecting to distant servers. This works by overcoming CPU limitations affecting VPN protocol processing and using advanced networking techniques to reduce latency. Faster connections mean you’re more likely to keep the VPN active rather than disconnecting for better performance. This technology makes a real difference when you’re looking for the best regions for cheap Steam games, geo-hopping for better lobbies, etc.
- Alternative routing helps defeat censorship by routing connections through third-party networks like AWS when direct access to Proton servers is blocked. This ensures you can establish a VPN connection even in countries that actively try to prevent VPN use.
- Split tunneling, available on Windows and Android, lets you route specific apps or IP addresses through the VPN while excluding others. This is useful for activities like online banking that may flag VPN connections while keeping your general browsing protected.
Free Plan: No Compromises on Security
Proton VPN offers a genuinely free tier with no ads, no data limits, and the same security protections as paid plans. This is unusual in the VPN industry, where free services typically monetize users through advertising or selling data.
The free plan is subsidized by paid subscribers who gain access to additional features like servers in 120+ countries, higher speeds, Secure Core, streaming support, and P2P file sharing. Free users get servers in select countries and one device connection, but crucially, they receive the same encryption, no-logs policy, and kill switch protection. If you’re using a VPN primarily for gaming platforms, our guide on the best Steam VPNs covers which services work best with Valve’s platform.
This model works because Proton’s parent company also operates Proton Mail, the world’s largest encrypted email service. The VPN was originally created to ensure Proton Mail users could access their email, even in countries that block the service. Providing free VPN access serves Proton’s mission of making privacy accessible to everyone, particularly those who need it most but may not be able to afford paid services.
Company Transparency and Ownership

Unlike many VPN providers that hide behind offshore shell companies, Proton operates with full transparency about its ownership and leadership. The company is headquartered in Geneva, Switzerland, with its address, company statutes, and directors all publicly available for inspection in the Swiss commercial registry.
Proton’s origins are well-documented, from the founding by scientists at CERN to the initial crowdfunding campaign that helped launch Proton Mail. The scientific background of the leadership team is a matter of public record, including academic careers and published research papers.
The Proton Foundation, a non-profit organization dedicated to advancing online security, privacy, and freedom, is Proton’s primary shareholder. This ownership structure ensures the company remains focused on its mission rather than maximizing shareholder returns. Proton is entirely community-funded, with no venture capital investors or advertisers influencing its direction.
Performance Considerations
Security features mean little if the VPN is too slow to use. Proton VPN operates one of the fastest networks available, with servers capable of 10 Gbps speeds and VPN Accelerator technology addressing the performance penalties typically associated with encrypted connections.
WireGuard protocol delivers the best speeds, with minimal overhead compared to older protocols. Most users will find Proton VPN fast enough for streaming, gaming, and general browsing without noticeable slowdown. For bandwidth-intensive titles, our guide on the fastest VPNs for gaming includes Proton VPN among the top performers for long-distance connections.
The server network spans every continent with 15,000+ servers in over 120 countries. This geographic diversity means you can usually find a nearby server for optimal speeds while still maintaining access to content from virtually any region.
Who Is Proton VPN Best For?

Proton VPN excels for users who prioritize verifiable privacy over marketing claims. If you need a VPN with documented, audited security practices backed by real-world legal testing, Proton delivers what most competitors only promise.
The service is particularly well-suited for journalists and activists operating in hostile environments, with Secure Core providing protection against sophisticated surveillance.
Privacy-conscious users who want to verify rather than trust will appreciate the open-source code and published audit reports. Anyone in or traveling to countries with censorship will benefit from Stealth protocol and alternative routing capabilities. My full guide on the best VPNs for China gives you even more great options.
For gamers specifically, Proton VPN’s speed and Secure Core protection against DDoS attacks make it a solid choice. For streaming, the service supports all major platforms with dedicated servers optimized for video playback.
Proton Is One of the Safest VPNs Out There
Is Proton VPN safe? Based on verifiable evidence rather than marketing claims, yes.
We have a combination of:
- Swiss jurisdiction preventing forced logging
- Four consecutive annual no-logs audits by independent experts
- Open-source code subject to community scrutiny
- Strong encryption using only proven protocols
- Real-world legal testing confirming logs don’t exist
- Transparent ownership with documented company history
- Additional protections like Secure Core and kill switch on all platforms
This incredible list makes Proton VPN one of the most trustworthy VPN services available, and, I would say, one of the best VPNs as well.
No VPN can provide absolute anonymity, and Proton is honest about this. Their documentation clearly states the threat model for their services and what they can and can’t protect against. This transparency itself is a security feature: when a company is upfront about limitations, you can make informed decisions about whether their protection matches your needs.
For users who want privacy they can verify rather than privacy they must take on faith, Proton VPN delivers exactly that.
FAQs
No major security breaches have been reported. Proton’s open-source code and regular independent audits help identify and fix potential vulnerabilities before they can be exploited. The company also operates a bug bounty program that incentivizes security researchers to responsibly disclose any issues they discover.
Yes, Proton VPN’s Stealth protocol is designed to bypass censorship, including China’s Great Firewall. The protocol disguises VPN traffic as regular HTTPS, making it difficult to detect and block. Alternative routing through third-party networks provides additional circumvention options when direct connections are blocked.
Yes. Free users receive the same encryption, the same no-logs policy, and the same security features as paid subscribers. The only differences are fewer server locations, one device connection, and no access to premium features like Secure Core or streaming optimization. Security is not compromised.
Proton can only respond to legally binding requests from Swiss courts. Foreign requests must go through formal international channels. Even if compelled to provide data, Proton’s audited no-logs policy means there’s no user activity information to hand over. Their transparency report documents all requests received and their responses.